Vulnerability Assessments | Cyber Security Services
Detect.
Vulnerability Assessment
Identify your vulnerabilities and report back on potential exposures.
A Vulnerability Assessment is an automated engagement that actively scans internal and external infrastructure (including all systems, network devices and communication equipment connected to that network) for vulnerabilities that could be exploited by cybercriminals.
Similar to Penetration Testing, but mainly leveraging automated systems and scanning tools, Vulnerability Assessments provide a high-level view of risks over a larger area of your network, in a shorter amount of time, and for a lower cost.

Is a Vulnerability Assessment Right for My Organisation?
A CyberLab vulnerability assessment is the first step to protecting your data and the place to begin if you have never undertaken any security testing.
We offer two types of vulnerability assessments:
We keep a constant eye on your security, so you don’t have to. CyberLab’s vulnerability scanner regularly scans your systems for emerging vulnerabilities and identifies weaknesses in your digital infrastructure to avoid costly data breaches.
You can automate your monthly vulnerability assessments with CyberLab Control, our flagship Cyber Security-as-a-Service (CSaaS) platform. We’ll automatically scan your systems, analyse the results, and provide you with a full report and recommendations.
Types of Vulnerability Assessment
CREST-Approved Semi-Automated Vulnerability Assessment
Performed by one of our CREST-approved penetration testers who will run some automated tests, then analyse and review the output of automated tests, manually merge issues, and run manual checks to reduce false positives.
Depending on your requirements, these tests may include:
- External Vulnerability Assessments (Unauthenticated)
- Internal Vulnerability Assessments (Unauthenticated & Authenticated)
- Workstation and server patch checking sweeps (Authenticated)
Fully-Automated Vulnerability Assessment
We keep a constant eye on your security, so you don’t have to.
CyberLab’s vulnerability scanner regularly scans your systems for emerging vulnerabilities and identifies weaknesses in your digital infrastructure to avoid costly data breaches.
You can automate your monthly vulnerability assessments with CyberLab Control, our flagship Cyber Security as a Service (CSaaS) platform. We’ll automatically scan your systems, analyse the results, and provide you with a full report and recommendations.
Vulnerability Assessments vs Penetration Tests
What is the Difference?
Vulnerability Assessments identify system and software vulnerabilities and provide a high-level overview of your security posture. It is an effective way for companies who do not have visibility of their posture to gain a more complete understanding. For organisations with legacy infrastructure, it is a quick, cost-effective way to identify easily quick-wins when it come to patching software and systems.
A Penetration Test not only identifies security issues within the company’s infrastructure and systems, but also exploits these vulnerabilities to achieve a specific objective. For example, if the objective is to gain internal network access, we might identify a vulnerability that allows us to upload files, then another one that lets us find those files, and another one that marries these up to execute something malicious.
It’s not the testing process that matters the most – it’s implementing the remediation actions from the reports to proactively improve your security posture.
Vulnerability Assessment Comparison Table
CyberLab Control | Cyber Security as a Service
Free 14-day Trial
- Vulnerability Scanning
- Security Awareness Training
- Phishing Simulation Campaigns
- Dark Web Monitoring
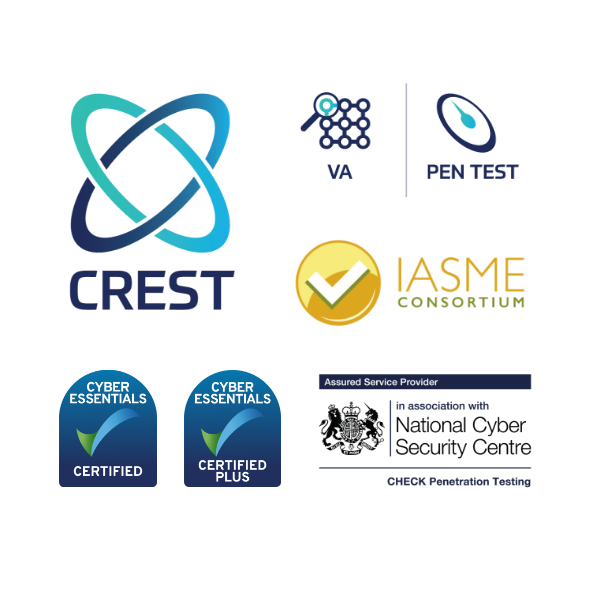
Our Accreditations & Qualifications
CREST (the Council of Registered Ethical Security Testers) is an international accreditation with a strict Codes of Conduct and Ethics. CHECK is the Government-backed accreditation from the National Cyber Security Centre (NCSC) which certifies that a company can conduct authorised penetration tests of public sector systems and networks.
With decades of combined experience, our team and take pride in operating at the highest level of the industry and always aim to go the extra mile.
CyberLab Accreditations
Cyber Essentials Plus
Cyber Resilience Centre Trusted Partner
IASME Consortium Gold Certified Company
CREST PEN TEST certified
CREST VA certified
Penetration Tester Accreditations
CREST Practitioner Security Analysts
CREST Registered Penetration Testers
CREST Certified Web Application Testers
CREST Certified Infrastructure Testers
CHECK Team Member
CHECK Team Leader – Infrastructure
CHECK Team Leader – Applications
Speak With an Expert
Enter your details and one of our specialists will be in touch.
Whether you’re looking to implement basic cyber security best practice, improve your existing defences, or introduce a new system or solution, our team of expert consultants, engineers, and ethical hackers are here to help.
Our team specialise in creating bespoke security solutions and testing packages to improve and maintain your security posture.
We are 100% vendor agnostic and will only ever recommend the best products and solutions for your requirements.